Operational Impact Assessment
Identify Critical IT Assets to Strengthen Resilience and Guide Smarter Cybersecurity Investment
Don't Find Out the Hard Way
$4.4 Million
The average cost of a data breach, according to a 2025 IBM Report
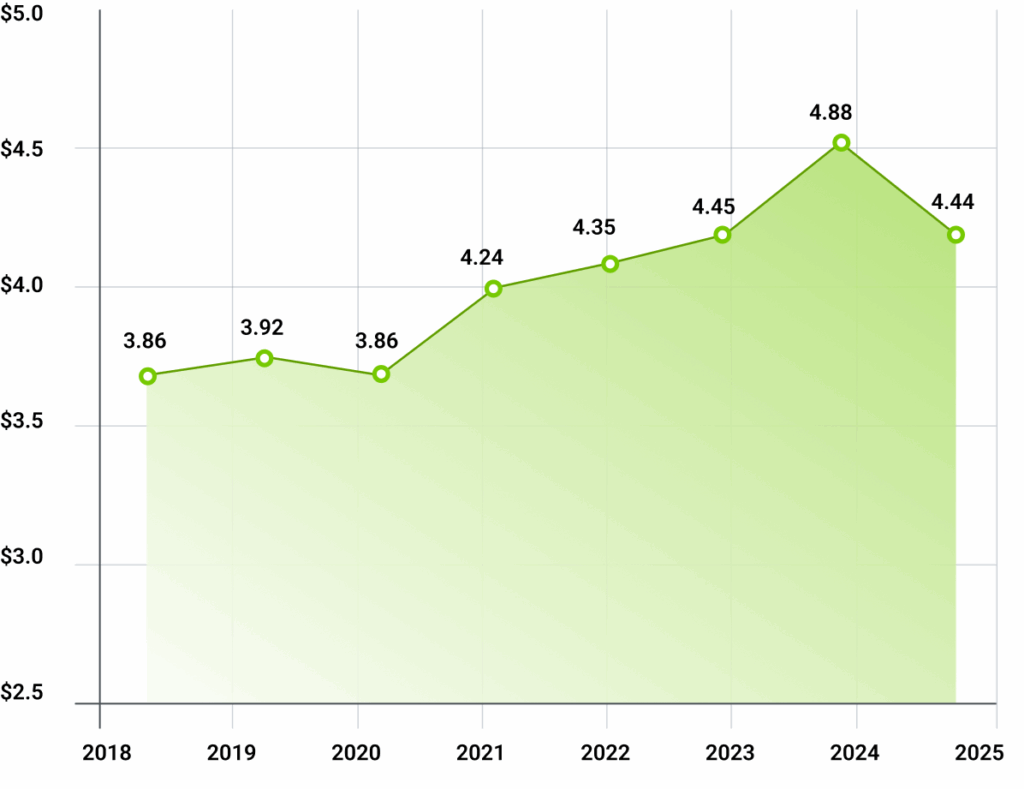
2025 IBM Data Breach report
OIA Impact
530+
Critical Assets Identified
32
Organizations Served
1.5M+
Coloradans Impacted
What is an OIA?
Think of the OIA as the GPS for your organization’s cybersecurity and disaster recovery efforts.
By mapping IT assets to business processes and objectives, the assessment identifies single points of failure that could disrupt operations.
This insight guides informed cybersecurity and resilience investments helping organizations protect what matters most.
How It Works
1
Identify Business Objectives
Define your organization’s mission and the business processes that support it.
Clarify what your organization must achieve, and which core processes are essential to mission success.
2
Map IT Assets to Business Processes
Connect critical IT assets to the processes they enable.
Identify the systems, applications, and infrastructure required to support day-to-day operations and organization-wide objectives.
3
Identify Critical Assets
Reveal single points of failure and operational risk.
Determine which assets are most critical by identifying dependencies and potential failure points that could disrupt operations.
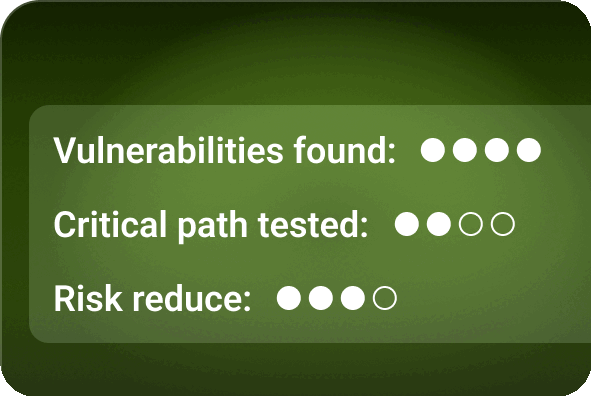
Deliverables
Impact Analysis
Evaluation of how cyber asset failures would affect your organization’s mission and each department’s critical task
Critical Cyber Asset Inventory List
A list of the most important cyber assets, such as software and hardware, ranked by how essential they are to operations.
Dependency Maps
A visual of how your critical assets rely on one another, so you can spot single points of failure before they can cause disruption.
Tabletop Exercises
Simulations based on the potential failure scenarios revealed by the assessment to improve response, recovery, and executive-level decision-making in a crisis.
“This thorough evaluation encompassed identifying the cyber assets that are mission-critical to our success, allowing our team to have confidence we are focusing on the correct assets to enhance our security posture. The NCC’s meticulous approach ensured a seamless process, and the actionable insights provided have been invaluable to our team.”
-Robert Losinski (Manager of Information Security, Denver Public Schools)